PHP Advent Calendar Day 21
21 Dec 2007Today's entry, provided by Luke Welling, is entitled Following the Big Dogs on Web Application Security.

- Name
- Luke Welling
- Blog
- lukewelling.com
- Biography
- Luke Welling is from Melbourne, Australia, but currently lives near Washington, DC, where he ekes out a living as a security nerd at OmniTI. He sees lots of good PHP and bad PHP, and tries to write more good than bad. Over the last decade, he has applied PHP in many places where it was intended, and in many places where it was never meant to go. With his wife Laura, he wrote the bestselling book PHP and MySQL Web Development and often speaks about PHP at conferences and user groups. His hobbies include riding his horses and sticking Splayds in toasters, although he has not yet attempted to do both at once.
- Location
- Washington, District of Columbia
At this time of year, people are apt to get all warm and sentimental, right up until their first trip to a mall on a Saturday when they go back to hating their fellow man and instituting an "If Amazon don't sell it, you're not getting it" policy on gift giving. December is very important to retail, and very important to retail sites.
I remember some good advice I read a long time ago. Vincent Flanders & Michael Willis in Web Pages That Suck suggested you "follow the big dogs." In other words, copy Amazon. Their reasoning was sound. You will likely get it wrong on your first try, you can't afford to run usability studies of your own, and don't want to spend months and numerous iterations getting it right. Learning from other people's mistakes is always less embarrassing than learning from your own.
I have had to paraphrase here, because I opted to recycle nearly all my old books rather than ship them half way around the world. Had I wanted to check the accuracy of my quote, it would have cost me one cent to buy a second-hand copy of that book.
While the long-term relevance of most of the advice in old computer books is fairly accurately reflected by that valuation, it was good advice in 1998. If you were embarking on an ecommerce venture at a time when there was a shortage of people who knew what they were doing, best practice conventions were not settled, and innovation was rapid, there were worse philosophies you could have than "What Would Amazon Do?"
The same idea is popular today, and for the same reason. There is always a shortage of people who really know what they are doing, so there are plenty of people making decisions by asking "What Would Google/Amazon/Microsoft/eBay/PayPal/Flickr/Yahoo/YouTube/Digg/Facebook Do?" If you are in a space where nobody really knows the best way yet, copying the segment leader is a low risk, low talent shortcut to making mainly good decisions, even if does mean you are always three months behind.
The idea does not apply well to web application security. There are two main reasons for this: first, the big dogs make plenty of mistakes, and second, good security is invisible.
You might notice mistakes, you might read about exploited vulnerabilities, and you might notice PR-based attempts at the illusion of security, but you probably don't notice things quietly being done well.
Common big dog mistakes include:
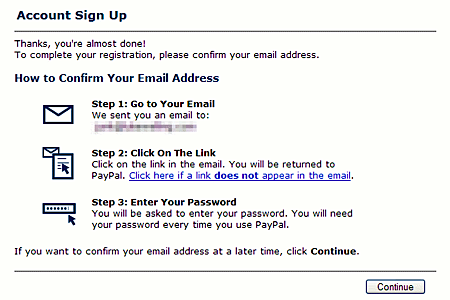
- Inviting People to Click Links in Email Messages
- You would think that, as one of the most popular phishing targets out there, PayPal would not want to encourage people to click links in emails. Yet, if you sign up for a PayPal account, the confirmation screen requests that you do exactly that:
- Stupid Validation Rules
- We all want ways to reject bad data, but it is usually not easy to define hard and fast rules to recognize it, even for data with specific formatting. Everybody wants a simple regex to ensure email addresses are well formed. Unfortunately, to permit any email that would be valid according to RFC 2822, a simple one is not going to cut it. As a result, many people add validation that is broken and reject some real addresses. Most are not as stupid as the one AOL used to have for signing up for AIM, which insisted that all email addresses end in
.com,.net,.org,.edu, or.mil, but many will reject+and other valid non-alphanumeric characters in the local part of an address (the bit before the@). - Stupid Censorship Systems
- Simple keyword-based censorship always annoys people. Eventually, somebody named Woodcock is going to turn up. Xbox Live is infamous for rejecting gamertags and mottos after validating them against an extensive list of "inappropriate" words. Going far beyond comedian George Carlin's notorious Seven Dirty Words, there is a list of about 2,700 words that are supposedly banned. By the time you add your regular seven, all possible misspellings thereof, most known euphemisms for body parts, racial epithets, drug-related terms, Microsoft brand names, Microsoft competitors' brand names, terms that sound official, and start heading off into foreign languages, you end up catching a lot of innocent phrases.
- Broken HTML Filtering
- Stripping all HTML from user-submitted content and safely displaying the result is often done badly, but is not that difficult. On the other hand, allowing some HTML formatting as user input, but disallowing "dangerous" parts is not an easy problem, especially if you are trying to foster an ecosystem of third party developers. The MySpace Samy worm worked not because MySpace failed to filter input, but because of a series of minor exploits that, combined, allowed arbitrary JavaScript. Once you choose to allow CSS, so that users can add what passes for style on MySpace, it becomes very hard to limit people to only visual effects. eBay has had less well-known problems with a similar cause, but without a dramatic replicating worm implementation. Earlier this year, scammers were placing large transparent
divs over their listings, so that any click on the page triggered amailtoor loaded a page of their own. I could not see examples today, so I assume they have fixed the specific vector, but giving users a great deal of freedom to format the content that they upload makes ensuring that content is safe for others to view very difficult. - Stupidly-Long URLs
- The big dogs love long, complicated URLs.
https://chat.bankofamerica.com/hc/LPBofA2/?visitor=&mses
sionkey=&cmd=file&file=chatFrame&site=LPBofA2&channel=we
b&d=1185830684250&referrer=%28engage%29%20https%3A//site
key.bankofamerica.com/sas/signon.do%3F%26detect%3D3&sess
ionkey=H6678674785673531985-3590509392420069059K35197612
Letting people get used to that sort of garbage from sites that they should be able to trust, you can't really be surprised when normal people can't tell the difference between an XSS attack hidden in URL-encoded JavaScript and a real, valid, safe URL. Even abnormal people who can decode a few common URL encodings in their heads are not really scrolling across the hidden nine tenths of the address bar to look at all that. - Looking for Simple Solutions
- Security is not one simple problem, or even a set of simple problems, so looking for simple solutions such as the proposed
.bankTLD is rarely helpful. This is not helped by the vendor-customer nature of much of the computer industry. The idea that you can write a check to somebody and a problem goes away is very compelling; buy a more expensive domain name, or a more expensive Extended Validation Certificate, or run an automated software scan to meet PCI compliance and you might sleep more soundly at night, but many users already don't understand the URL and other clues that their browser provides them. Giving more subtle clues to them is unlikely to help. Displaying a GIF in the corner of your web page bragging about your safety might create the illusion of security and might well help sales, but it won't actually help safety on its own.
You can't follow the public example of the big dogs. They still make some dumb decisions, they still make the small mistakes that allow the CSRF and XSS exploits that are endemic, and they are often not very responsive to disclosures. If a major site makes 99 good security decisions and one bad one, you won't notice the 99. Unfortunately, with security, you are still far better off seeing how others have been exploited and critically evaluating what they say they should be doing, rather than trying to watch what they actually are doing.
Oh, and remember to stay away from malls on weekends in December.

