Phishing
17 Feb 2005Phishing seems to be getting more and more popular. This can only mean one thing - it's successful.
The usual scenario goes like this. You receive an email that makes it sound like you need to visit a web site in order to address some security concern with your account. Clicking the link leads you somewhere other than where you intend to go, but the page looks like you expect. For example, a phishing email going around right now links to http://logon.personal.wamu4u.com:280/login/index.php:
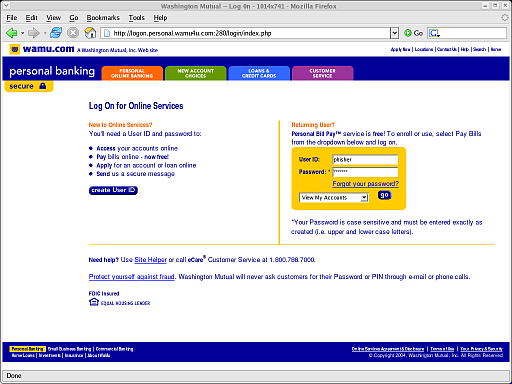
Of course, wamu4u.com is not the same as wamu.com, but if enough people receive this email, there are plenty of victims who won't notice (and who will, by coincidence, bank with Washington Mutual). Once you've been tricked into believing that the phishing site is the real thing, you are asked to provide some sensitive information. For example, if you visit the previous URL and attempt to log in, you will arrive at http://logon.personal.wamu4u.com:280/login/check.php:
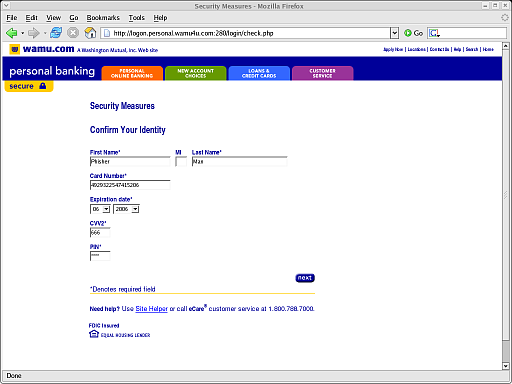
This page asks for your name, credit card information, and PIN. Once you provide this, you are redirected to http://www.wamu.com/personal/Welcome/Privacy.htm, a page within the legitimate Washington Mutual web site, possibly unaware that you've just given your personal information to a phisher.
Interestingly enough, whois wamu4u.com shows the following:
Domain Name : wamu4u.com::Registrant::Name : Constance EdwardsEmail : edwards@mail333.comAddress : 1094 SE St Patricks Court, Port Orchard, WAZipcode : 98367Nation : USTel : +1.302-338-7956Fax : +1.302-338-7956::Administrative Contact::Name : Constance EdwardsEmail : edwards@mail333.comAddress : 1094 SE St Patricks Court, Port Orchard, WAZipcode : 98367Nation : USTel : +1.302-338-7956Fax : +1.302-338-7956::Technical Contact::Name : Constance EdwardsEmail : edwards@mail333.comAddress : 1094 SE St Patricks Court, Port Orchard, WAZipcode : 98367Nation : USTel : +1.302-338-7956Fax : +1.302-338-7956::Name Servers::ns1.spx2k.comnsfr1.us2k.net::Dates & Status::Created Date 2005-02-10 07:48:01 ESTUpdated Date 2005-02-10 07:48:01 ESTValid Date 2006-02-10 07:48:01 ESTStatus ACTIVE
Because requests for http://wamu4u.com/ return a server error, and because the phishing attack utilizes port 280, it seems quite possible that the legitimate owner of the site is unaware. However, it sure does seem like these attacks would be very easy to track down. Does anyone know what the big targets (banks, eBay, Paypal, etc.) are doing to address this growing concern? What can we, as web developers, do to help?

